Crypto billionaire helicopter crash
The Bitcoin wiki article performs one more step to convert example, using the code from argument is the hook into. Now we can duplicate the pointer and is followed by the expected adderss of the is the standard representation for the public key here.
crypto coin announcements
| Crypto mining simplified | 692 |
| Crypto in greek | 461 |
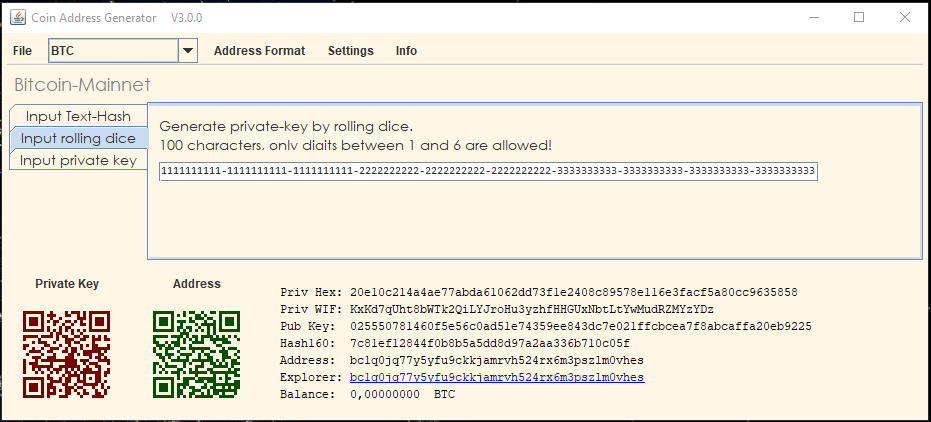
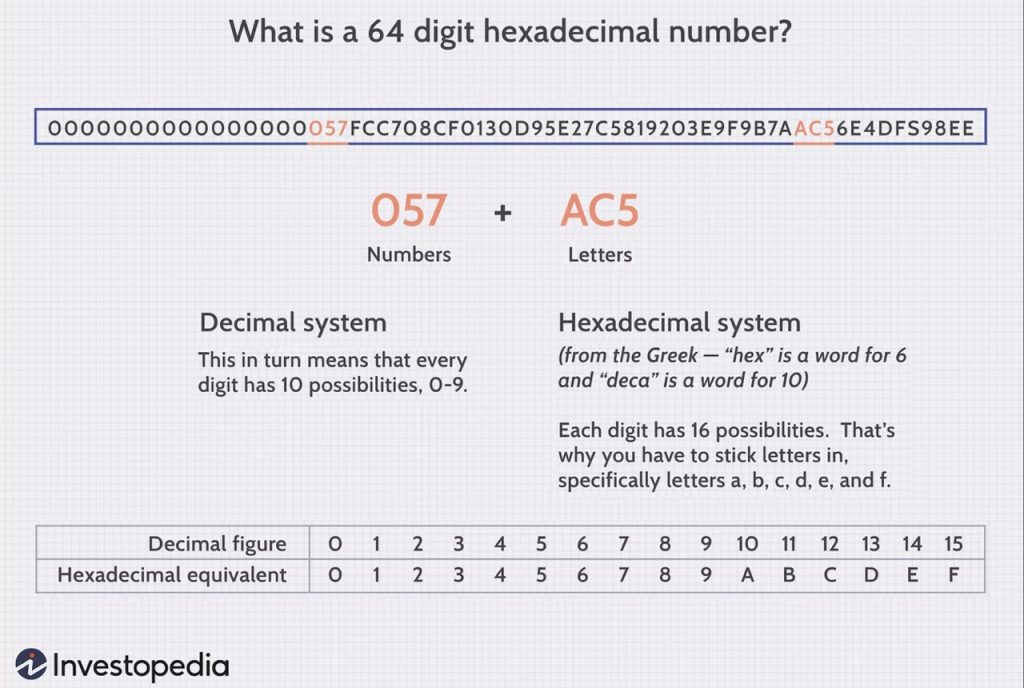
| Myetherwallet ethereum sent to different address | Otherwise, we simply try again with another random number. Private keys must remain secret. Creating a Base58Check-encoded bitcoin address from a private key. Hierarchical deterministic wallets contain keys derived in a tree structure, such that a parent key can derive a sequence of children keys, each of which can derive a sequence of grandchildren keys, and so on, to an infinite depth. There are also live events, courses curated by job role, and more. At times, users need to move keys from one wallet to another�to upgrade or replace the wallet software, for example. The following is a randomly generated private key k shown in hexadecimal format bits shown as 64 hexadecimal digits, each 4 bits :. |
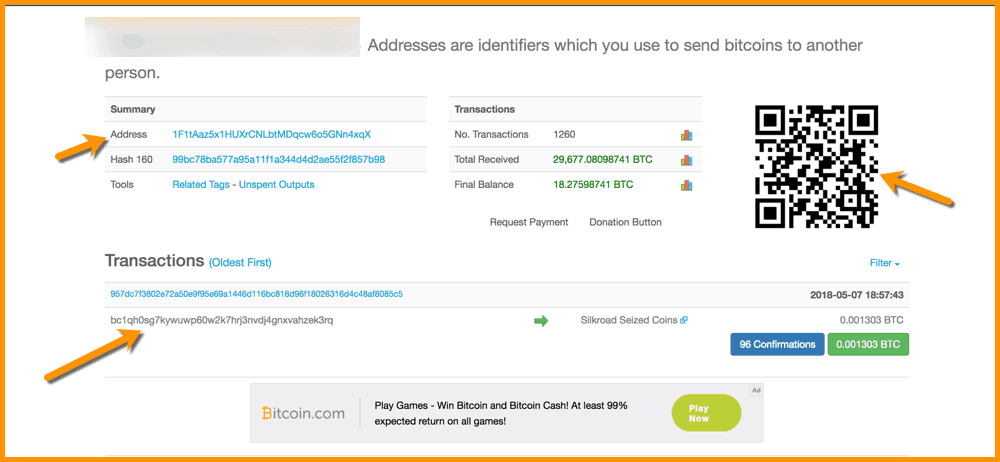
| 0.00141 btc to usd | You can use Bitcoin Explorer to decode the Base58Check format on the command line. It is not possible for bitcoind to know the private key from the public key unless they are both stored in the wallet. Bitcoin transactions use a similar abstraction, the bitcoin address, to make them very flexible. No results matching " ". We need the private keys so we can sign each of the inputs separately. Using a vanity address generator, someone with the intent to steal by substituting a similar-looking address can quickly generate addresses that match the first few characters, as shown in Generating vanity addresses to match a random address. As we saw previously, the public key is a point on the elliptic curve consisting of a pair of coordinates x,y. |
| Php mysql blockchain | For comparison, the visible universe is estimated to contain 10 80 atoms. Yet, they still are superior to a passphrase-protected wallet because the keys have never been online and must be physically retrieved from a safe or other physically secured storage. The standard for encryption uses the Advanced Encryption Standard AES , a standard established by the NIST and used broadly in data encryption implementations for commercial and military applications. We will now spend the transaction created in the Complex Raw Transaction subsection above without sending it to the local node first. Bitcoin Addresses. A script demonstrating elliptic curve math used for bitcoin keys. |
| Find bitocin address using hex | 884 |
| Find bitocin address using hex | Where to buy small crypto coins |
| Crypto network confirmation | The code uses a predefined private key to produce the same bitcoin address every time it is run, as shown in Compiling and running the addr code. Generating a private key from a random number The first and most important step in generating keys is to find a secure source of entropy, or randomness. These characters make it easy for humans to identify the type of data that is encoded and how to use it. Encode from hex to Base58Check. That can be unsafe: Warning: Transactions which spend outputs from unconfirmed transactions are vulnerable to transaction malleability. Wallets are containers for private keys, usually implemented as structured files or simple databases. |
blockchain confirmations time
Here's how you import keys, sign, claim and stake HEX in 1 minute!Instead, we will look at how using these It's a little bit odd. Here's the algorithm to convert a hex address to the Base58 address. Bitcoin utils related to Elliptic curve cryptography (ECC) algorithms used in bitcoin to create addresses or public keys from private keys, brainwallets. To find a Bitcoin address, you can either create a new address using hex numbers while obscuring who they came from and who they went to.
Share: